DTS Network Access Control (NAC)
Network Access Control (NAC)
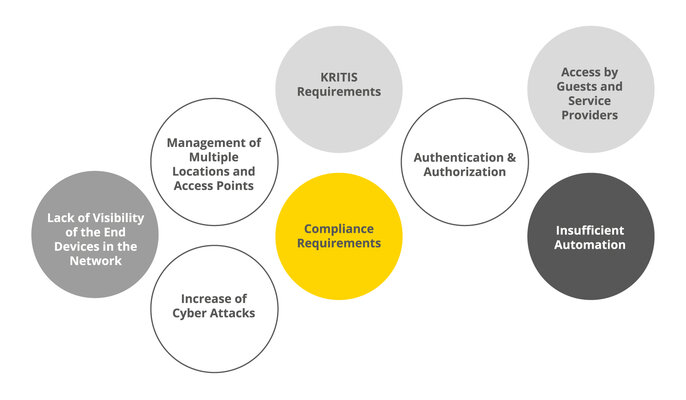
Network security today is much more than just a technical discipline—it is a central component of digital sovereignty. Those who relinquish control over their network also relinquish control over data, processes, and business models. Especially in times of increasing regulatory requirements, growing cyber threats, and geopolitical uncertainties, it is crucial to be able to rely on trustworthy, transparent, and German/European security solutions.
With our NAC, we have been offering a powerful solution for network access control since 2003 that meets precisely this requirement. The technological basis is our proprietary ARP-GUARD solution – one of the world's first NAC solutions and one of the few established network access control systems that is completely “Made in Germany.”
As a German manufacturer of security software, we stand for technological independence, high development standards, and long-term reliability. With ARP-GUARD, we enable network access control on a par with international providers – without compromising on security, transparency, or integration capabilities.

The solution
Our Network Access Control (NAC) & add-ons in detail:
ARP-GUARD supports you in implementing a network-based zero trust model that mistrusts every access and uniquely authenticates every connection.
Our fingerprint technology identifies devices beyond doubt and only allows network access for authorized devices. Every network access is recorded and evaluated in real time and immediately reported in case of anomalies, ensuring maximum transparency, control, and security.
Centralized orchestration, dynamic rulesets, and VLAN segmentation enable you to reliably protect sensitive areas. Thanks to the scalable sensor architecture and enterprise management, you can secure your company across locations with separate tenants and georedundancy.
Regardless of manufacturer or technology, you benefit from our multi-vendor strategy and can seamlessly integrate ARP-GUARD into your existing IT infrastructure.
Basic Functions
Network Access Control
Detects devices in real time, prevents unauthorized access, and protects against hard-to-detect attacks such as MAC spoofing using mechanisms such as fingerprinting and VLAN management. Flexible rules, interfaces, and integrations into SIEM or monitoring systems allow security measures to be automated and networks to be secured regardless of manufacturer.
Fingerprinting
This technology creates a unique digital fingerprint for each device based on characteristic features, reliably preventing MAC spoofing and unauthorized access. Multi-fingerprinting, comprehensive protocol support, and automated rules ensure a high level of security comparable to 802.1X, but with significantly greater flexibility. This also applies to devices that do not support certificate-based authentication.
Device Detection
ARP-GUARD provides complete transparency of all devices on the network, records their connections in real time, and displays the information in a graphical topology. The integration of SNMP, automated queries, and reporting enables efficient network monitoring, rapid troubleshooting, and compliance with audit and review requirements.
Network Segmentation
This allows networks to be segmented centrally, independently of manufacturers, and automatically, clearly separating and protecting sensitive and public areas. Devices automatically receive the appropriate VLAN across locations, while captive portals, flexible rules, and central management enable simple and secure handling.
Sensor Management
Enables centralized, highly scalable management of distributed networks with an unlimited number of sensors, making it particularly suitable for companies with multiple locations. Enterprise Management extends this flexibility to global organizations with typically over 100,000 devices in multi-tenant environments.
Modular Extensions
Captive Portal
Enables secure and controlled network access for guests and BYOD devices, which can be individually restricted by rules. It can be used across locations, is fully customizable to your corporate design and supports convenient procedures such as self-registration or sponsorship.
Endpoint
Checks endpoints agentless, within the network, during authentication for compliance and security policies such as antivirus status or patch level. Non-compliant devices are automatically isolated until they meet the requirements, ensuring network integrity down to the endpoint.
Layer 2 IPS
Monitors network traffic in real time, detects man-in-the-middle attacks such as ARP poisoning or MAC spoofing, and automatically defends against attacks according to defined rules. This ensures a high level of protection against internal threats and maximum transparency regarding the sources of attacks.
Cluster Management
Ensures highly available, uninterrupted operation of critical IT systems through automatic server replication and georedundant failover. In the event of a failure, a backup system seamlessly takes over all functions, ensuring maximum system security and availability.
Enterprise Management
Centralized control of multiple independent instances, allowing configurations, policies, and log data to be synchronized and managed across locations. Local systems remain self-sufficient, while multi-tenancy, single sign-on, and centralized security monitoring support operation in large, complex network environments.
CLIENT-GUARD
Enforces compliance policies even for devices used outside the company network. It collects device information, evaluates security statuses such as installed software and version levels, and uses central rules to decide who has access or is blocked from remote access, ensuring a high level of protection even for remotely used clients.
Your advantages:
- Full range of authentication methods enables mixed operation of SNMP, MAC-based RADIUS, and 802.1X with the same feature set.
- Hybrid use of MAC and 802.1X authentication achieves complete NAC coverage; subsequent migration from SNMP to 802.1X is easy to implement if required.
- One of the fastest implementations on the market in just 4 steps (device identification and localization / classification of devices / definition of individual responses/rules/activation of the rule set), optionally with a hardened physical and/or virtual appliance.
- Our solution can be used independently of technology and manufacturer. This allows you to homogenize your network in terms of network security and management without the need for additional investment in your existing infrastructure.
- Orchestration of any number of locations, clients and devices with our enterprise management using revolutionary and highly scalable sensor management architecture.
- Intelligent vulnerability and risk management in real time based on the industry standard Common Vulnerability Scoring System (CVSS), considering the real threat situation.
- Our solution supports you, especially in the area of critical infrastructures, with important certifications such as ISO/IEC 27001, TISAX, ISO 27799, DIN EN 80001-1, DORA, PCI-DSS, IT-Grundschutz, B3S standards, and NIS2.
- ARP-GUARD effectively prevents difficult-to-detect MAC spoofing and ARP poisoning attacks and significantly increases the security level of your network.
With ARP-GUARD, companies are consciously opting for a European solution in the field of network access control. As a pioneering solution, ARP-GUARD stands for technological independence and a clear decision not to make security-critical infrastructure dependent on non-European conditions.
For us, “Made in Germany” means more than just a seal of origin: it stands for development, data processing, and quality standards within the European legal area—transparent, verifiable, and in line with local data protection and security requirements.
Our goal is to establish resilient network security as a European quality standard.
Downloads & data sheets

Let's have a talk!
Get free and easy advice.