Security Awareness Training
Security Awareness Training
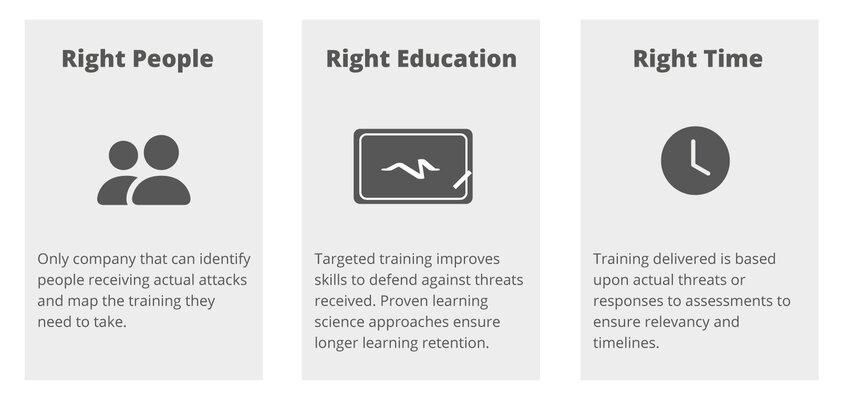
The modern threat landscape clearly has a number of human elements in addition to technical factors. This "human factor" is a popular target for cyberattacks. The majority of attacks on the human factor start with an email. There are technologies for detecting and blocking dangerous emails. However, the end user is the final security instance. They are the hurdle that must be overcome, because the security of sensitive company data stands or falls with them. For this reason, security awareness training is essential to reduce the likelihood of successful attacks, e.g. phishing or ransomware, through effective threat simulations and educational measures. Our Proofpoint Security Awareness Training (PSAT) is unique in this field and uses industry-leading risk intelligence and scientific learning principles to deliver the right training to the right people at the right time. We significantly strengthen your last line of defense "human factor".

The PSAT is based on a four-part methodology invented by three researchers and faculty members at Carnegie Mellon University. In their research for the National Science Foundation and the Department of Defense, they realized that traditional training methods were not effective in actually reducing risk and vulnerability to cyberattacks. Instead, they developed continuous training, with short, interactive and game-based training, as well as the use of simulated phishing attacks. This has proven to be more effective in changing behavior.
In the first step, the all-round security awareness training identifies the risk, who is under attack and what protection skills are available. For this purpose, ThreatSim and CyberStrength can be used to simulate attacks and to obtain basic knowledge. Proofpoint's industry-leading threat intelligence accesses data from billions of B2B and B2C emails. This allows realistic dynamic threat simulation phishing templates to be created. All in all, this creates a baseline measurement of the identity of the Very Attacked People (VAP) and the attacks they see. In this way, crucial priorities can be set.
In the next step, interactive training modules can be used to raise awareness in order to bring about changes in behavior. Proofpoint's training is unique in this respect. It is designed in response to actual threats and user behavior with learning science principles. The training content is continually updated to reflect evolving best practice and current attack trends identified through threat intelligence. The effective, interactive, video-based and gaming training modules encourage learners to close knowledge gaps about cyber security threats in the workplace and beyond. They also provide instant feedback.
As soon as your users are trained, they are able to report potential attacks. This reduces the attack surface. Closed-Loop Email Analysis and Response (CLEAR) further streamlines end-user reporting and security response to phishing attacks. This reduces the time required to neutralize an active threat. To this end, the email reporting button, PhishAlarm and the prioritization engine PhishAlarm Analyzer are connected to the Threat Response Auto-Pull (TRAP).
The PSAT is completed by the reporting tools. They provide all the information on end-user risks so you can focus on the areas, topics and best practices that will benefit you the most. The reports track user knowledge levels, overall performance of a phishing campaign, detailed information on user performance in each training module, and allow you to sort and filter all reports based on user-defined properties. These insights help administrators to target personalized training and achieve measurable results.
PSAT combines knowledge assessments, simulated attacks, interactive training modules, reporting and administration functions in a single, easy-to-use system. Of course, the entire platform can be used indefinitely during the license period to create any number of personalized training assignments and assign them at any time. Your administrators have full flexibility to deliver the right training to the right people at the right time. Customization options can be used to further individualize the training:
- Customization center
- Editing training content, incl. text/questions
- Add or remove images or questions
- Adding guidelines, certificates and more
- Module configuration
The assessments, simulated attacks and interactive training modules are available in more than 35 languages. The content is not simply translated. They are localized according to conventions. Elements such as domains, brands or logos, characters, currencies and regional references are linguistically appropriate and create a personal, relevant and engaging training experience for the end user.
DTS Managed Services
To ensure a successful introduction of the solution, we will take you by the hand if you wish. From planning the introduction to developing an individual training plan - you benefit from our numerous customer projects and best practices. After the successful introduction and initial planning of the solution, we take over the further administration of the platform for you and take care of the provision of the measures agreed in the training plan.
This includes the assignment of knowledge assessments and the coordinated training modules on various topics. We discuss the results of the measures, make adjustments to the training plan, plan phishing simulations and make further recommendations with you at quarterly scheduled jour fixe meetings. In order to create additional security awareness for real threats among your employees, we create simulated phishing messages for you, for example. These in turn can be used to show employees how deceptively real attackers are faking emails these days. Last but not least, we naturally provide you with German DTS support via a 9/5 hotline.

Let's have a talk!
Get free and easy advice.